Publishing Team Foundation Server 2005 (Single-Server Mode) with ISA Server 2006
Publishing a TFS within an ISA Server basically depends on creating three rules for web sites: One will use the TFS default port (8080), the second will use SharePoint (on port 17012) and the other one is for the common HTTP port (80).
A small comment about this: The same configuration described here, can also work for Team Foundation Server 2008.
It’s very important that you already have defined your public name for the TFS Server and even more important that this public name can be resolved by the ISA Server and over the Internet.
Let’s start then:
1 – Publish TFS Services
1.1 – Select “Publish Web Site” and use the proper name for that rule.

1.2 – Select “Publish a single Web Site or load balancer”.

1.3 – If you are not going to use SSL the just select “Use non-secured connections…”

1.4 – In this step you must indicate the FQDN that the clients will use to connect with the Team Foundation Server. Remember that this name should be already accessible for the ISA Server.

1.5 – No selection on Path and select “Forward the original host header…”

1.6 – Select “Accept Requests for: This domain name (type below)” and use the public TFS name again.

1.7 – On the next window you will need to create a Web Listener, which will be accepting the incoming requests for TFS Services port.

1.8 – Select again what kind of HTTP connections will use, secure or not secure.
1.9 – Select that the Listener will be getting the requests from the External network that you should already have on your ISA Server

1.10 Select that the Listener will not require authentication. This process will be done by the TFS itself.
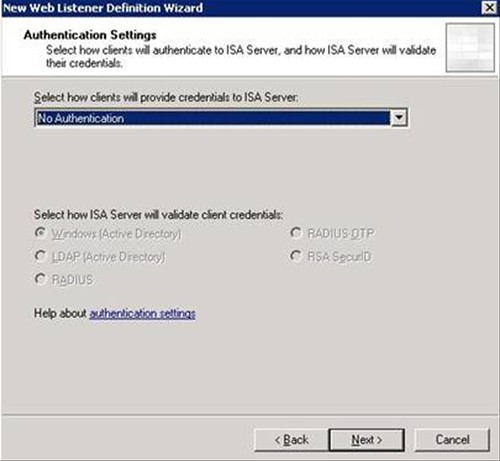
1.11 Hit Next and Finish the new listener creation.
1.12 Once that the creation of the listener finishes, you’ll be back at the rule wizard.
Leave selection of “No delegation, and client cannot authenticate directly”

1.13 Leave the “All Users” option and hit Next.
1.14 The wizard will complete but that’s not all. The web listener and the rules that you just created it actually didn’t complete with their proper configuration, all the listeners are created to “listen” in the default port of HTTP. Like TFS use the port 8080 to receive incoming requests, we will need to change that default port.
Access the rule properties and get to the “Bridging” and select the port 8080.

Now enter to the listener properties and select on “Connections” the correct port.

On “Authentication” select “Advanced” and check the option “Allow client authentication over HTTP”

1.15 Hit OK twice and the rule for TFS Services it’s ready.
2 – Publish TFS SharePoint
This rule follows the same configuration that the TFS Services on the steps 1 to 13. As you can imagine the differences are made within the ports configuration, and we will replace the 8080 used on the first rule by the 17012 of our SharePoint Services.
2.1 Enter the properties of the rule you just created for the SharePoint services and Access to the “Bridging” options and select the 17012 port.
Access the Listener properties and select “Connections” with the proper port:

Again on “Authentication” select “Advanced” and mark “Allow client authentication over HTTP”

2.2 Now the TFS SharePoint Rule it’s created.
3 – Publish TFS www
Like the other two rules, the steps from 1 to 13 are completely the same. Like this rule it’s representing an HTTP connection, neither ports on the Bridging option nor the Web Listener needs to be changed, they must keep as the default port 80 configured. The only thing that you must do is the authentication method, as we did on the first two.
3.1 “Authentication” select “Advanced” and “Allow client authentication over HTTP”

3.2 Hit OK twice and you are set to go.
That’s pretty much everything to do.
There’s a common issue within TFS public name. When you use this FQDN to connect over the Internet, it appears that the users have not the proper permissions, making the “Documents” and “Reports” items unavailable, for Team Explorer. You should check another post of mine that has the workaround for that problem.
Also here’s an interesting article about how ISA Server handles authentication:
http://technet.microsoft.com/en-us/library/bb794722.aspx
I hope you find it useful!
Cheers!
Categories: ISA Server, Team Foundation Sever



1 Comment »